An insider threat is the actions of an insider (employee, vendor, counterparty) aimed at using their authorized access to a company’s information or confidential documents in order to harm the organization. According to the Ponemon Institute, there are 3 types of insider leaks:
– Careless or negligent employee or contractor (56%)
– Criminal insider, including employee or contractor malice (26%)
– Employee/user credential theft (a.k.a. imposter risk) (18%)
All these actions, whether or not they are performed under the influence of some unscrupulous motive, nevertheless negatively affect the integrity, confidentiality and security of the organization, its data, personnel and/or facilities. In addition, such leaks can lead to both financial and reputational consequences.
In general, an insider threat, as defined by the Cybersecurity and Infrastructure Security Agency (CISA), is the threat that an insider will intentionally or unwittingly use their authorized access to harm the company’s mission, resources, personnel, facilities, information, equipment, networks, or systems.

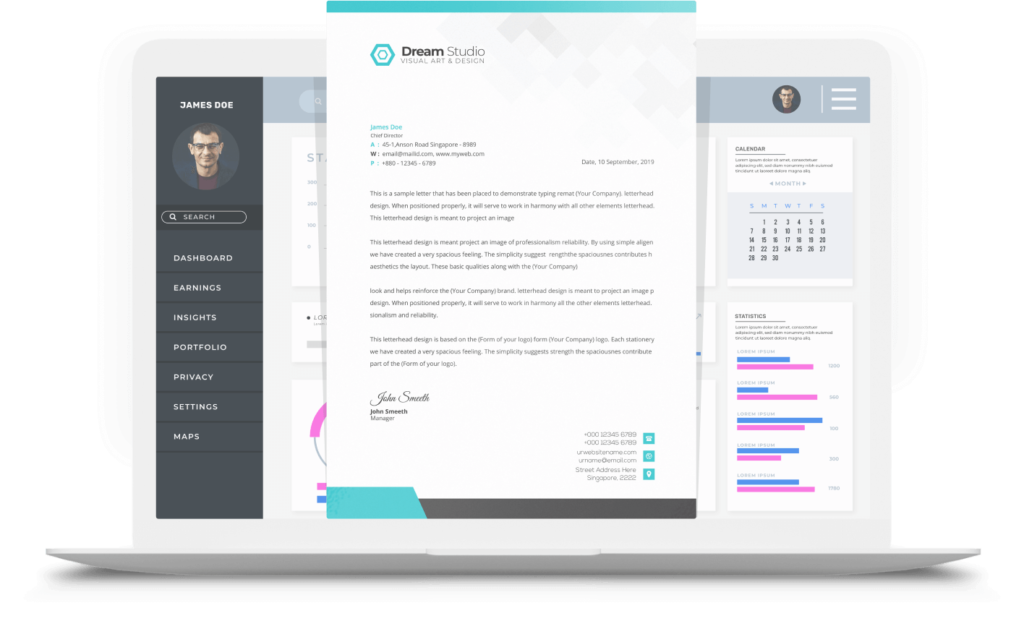
To counteract insider leaks, one option is to create a preventative effect; that is, make it common knowledge that leaks will be found, and leakers will be punished. LeaksID offers such an approach. Using the patented LeaksID technology, you can mark all confidential documents with invisible marks, using which, in the event of a leak, it is easy to determine the owner of the compromised copy.
For example, if someone simply takes a photo of a document open on the screen to which they have access, or a photo of a printed confidential contract, then the source can be identified by the markings. If everyone in the company knows that, no matter how they compromise a document, it will be possible to determine the source, the number and frequency of leaks themselves will decrease.
Try out LeaksID, our cloud solution to store documents, collaborate on them, and securely share them.