Google Drive integration is now available for all LeaksID users. It protects sensitive data in popular online storage from insider threats. Here is an overview of how it works.
Google Drive is one of the most prominent and widely used cloud platforms for document storage. Easy to learn but sophisticated system is highly trusted by numerous users and companies around the world. One of the most practical Google Drive features is the ability to provide file access using direct links.
However, while sharing links, the sensitive information is not protected from insider leakage. Suppose one of the users with granted file access wants to transfer it outside of a company. There are several ways to do it: link sharing, file download, a screenshot, or a picture of the screen with the information on it taken with a smartphone. In all these cases, the culprit stays undiscovered and unpunished, which means that it can happen again with other documents in the future.
To minimize the insider threat and deter a potential violator, we have developed LeaksID technology that can now be successfully integrated with Google Drive.

How LeaksID and Google Drive work together
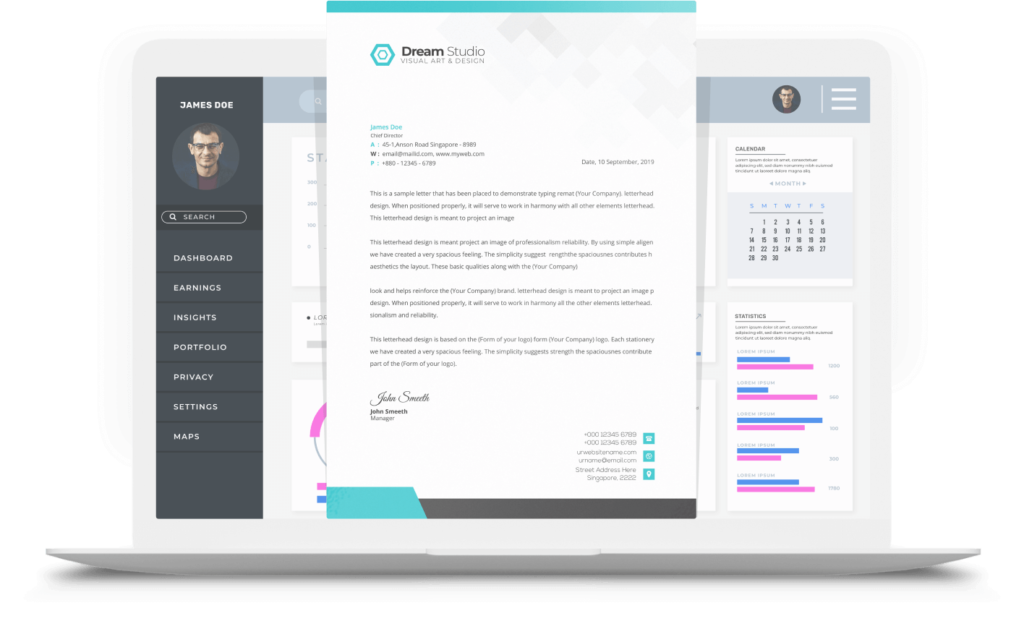
When the user with preinstalled LeaksID application right-clicks on a Google Drive document that needs to be shared, an option “Open with LeaksID” appears. After clicking on it, the user shall see a personalized protected copy in the automatically generated account on LeaksID (the original file remains on Google Drive).
Inside LeaksID, the owner of the document can grant different access rights to other users. However, all of them will interact not with the original file but with a personalized copy marked with the unique tags. These tags don’t interfere with the document workflow. They are invisible to a human eye and easily recognized by the system. Using these markers, the system can accurately identify who and when worked with a particular copy, and if a data breach occurs, it can determine the source.
A small fragment of even a damaged file is enough for a successful investigation. Due to the US-patented marking technology, the system can correctly identify the culprit from screenshots or pictures of the screen, and it was impossible before.

Who it is useful to
First of all, the integration with a popular file hosting service is efficient for company employees. With LeaksID, they don’t have to spend time retraining since they already know how to work with a familiar and comprehensible Google interface. This system will be especially helpful for law firms, companies involved in M&A deals, the healthcare sector, and screenwriters, as well as for other niche markets and government agencies. In these industries, any information leak threatens with multimillion losses and enormous reputational damage.
For example, let us recall the scandal with Mossack Fonseca, a major provider of offshore companies; its documents were leaked to the media in 2016. It turned out that among their users were leaders of 29 countries and billionaires from the Forbes list. After such a devastating blow to its reputation, the law firm could not recover and two years later announced its closure. Their clients also got compromised: after the publication of the documents, more than 150 investigations in 79 countries were opened on the facts of tax evasion and money laundering.
Most likely that if those who organized the data leak knew that they would be identified and discovered, they would abandon the whole idea. This is one of the key advantages of LeaksID: all users are aware that important information is protected by a solution that, in case of a leak, will identify its culprit. As a result, a culture of working with sensitive data based on a preventive effect is created: in organizations using LeaksID, the chance of leakage is minimized.
Leaks ID is now compatible with Google Docs, Sheets, and Slides. To learn more about LeaksID features for Google Drive, click here.
Stay tuned!
Try out LeaksID, our cloud solution to store documents, collaborate on them, and securely share them.