Companies often blame professional hackers for corporate data leaks. However, 56 percent of all personal data leaks in the world happen as a result of an employee’s error, according to the EY report released in 2019. Why does it happen? Is it possible to protect companies from threats created by their employees?
Companies are becoming increasingly aware that staff members play significant roles in endangering corporate secrets. Of IT specialists working in companies, 79 percent believe that it is employees’ faults that sensitive data is leaked. Of course, not all of them endanger corporate data on purpose. Cybersecurity breaches can be intentional and accidental.
Accidental violations
Phishing
Sometimes, unintentional corporate leaks happen because of employees’ negligence or unawareness. As happens most often, employees fall prey to phishing. Phishing refers to spreading e-mails infected with malware from sources disguised as verified and trusted.
Besides, many phishing websites disguise themselves as websites of well-known companies such as Facebook or various banks.
Masterminds of phishing attacks pursue the following goals: install malware on corporate computers to gain control of and manage them remotely and to steal usernames, passwords, banking information required to conduct a cyberattack.
Phishing is rapidly becoming a widespread type of cyberattack. According to Microsoft, the average number of phishing attacks per month increased by 350 percent in 2018. Last year alone, the number of companies that were compromised by phishing cyberattacks increased by 65 percent, and the number of hacked personal accounts increased by 70 percent.
Weak passwords
Weak passwords are the second-most widespread reason for corporate data leaks. In this respect, the numbers are shocking: according to a recent report by Verizon, more than 70 percent of employees use identical passwords. The report also specified that 81 percent of successful cyberattacks were made possible because weak passwords were stolen or cracked.
Free will
Another reason why employees endanger corporate data is that they willingly share it, oblivious to its secrecy. According to a poll conducted by Egress, 40 percent of employees think that their companies possesses exclusive rights to the data that they collect and store, while 29 percent of respondents firmly believe that they personally own the information they work with. These numbers demonstrate that most employees are not aware of how critical cybersecurity is for their companies. Only 25% of employees receive monthly updates from IT departments on the topic of cybersecurity.
Try out LeaksID, our cloud solution to store documents, collaborate on them, and securely share them.
Intentional violations
But why would employees leak corporate data deliberately? Reasons could vary from an impending layoff to resentment towards employers. Yet the most common reason why employees leak data is money. Seventy-five percent of data leaks in 2018 resulted from employees’ selfish desire to earn extra money, according to Verizon.
There are numerous ways to steal valuable information:
- Copying data to third-party removable storage;
- Transferring data via corporate or private email;
- Uploading data to cloud-based storage;
- Transferring data through social media and messenger apps;
- Stealing data by photographing screens or taking screenshots.
Solutions
For example, employees must always thoroughly check the domains of all websites they visit; they must not follow hyperlinks that look suspicious and must always verify the email address and sender’s name before opening an email.
Phishing emails often contain general greetings, a call to perform an urgent action, and hyperlinks embedded in the body of the message. Employees should think twice before sharing corporate data with a website they access by following such a link.
Three easy rules can help protect the company from its passwords being cracked.
- Always use different passwords for different accounts, separating professional from personal accounts.
- Change passwords regularly, at least once every few months. This security measure is easy yet very effective. A password-manager tool may help if you find this particular measure to be too tedious.
- A multi-factor authentication process also substantially decreases the risk of a security breach.
Technology can help to prevent intentional leaks of corporate data. For a long time, companies have been using data-leak-prevention (DLP) technology that monitors incoming and outgoing online traffic to protect corporate data. If an employee attempts to leak sensitive data via e-mail or removable storage, the system blocks the user’s suspicious action and notifies the security service of the company about the unauthorized attempt.
Yet DLP technology has several flaws.
For example, the system may slow down a workflow in the company if it blocks a suspicious transfer of confidential data. In addition, even though the DLP technology is an effective tool for analyzing incoming and outgoing traffic, it cannot protect companies against employees who leak data by photographing computer screens or by printing out sensitive documents. The DLP system cannot identify or pinpoint a specific breacher.
When it comes to photo and printing sensitive documents, DLP system fails to identify or pinpoint a specific breacher.
The Information Leaks Detection (ILD) system is a novel solution that complements the DLP technology. It is also known as Leaks ID in the United States.
The ILD technology can detect and pinpoint a specific breacher by creating individually marked copies of all files for each individual user. The system creates a new copy every time a document is being modified. The ILD system is capable of creating trillions of unique copies of a single Word or Pages document.
Even enterprises dealing with a large volume of documents will find this solution sufficient.
Visually, a modified copy does not differ from the original. Yet every element of the file contains unique tags that the system uses to identify a sender and a recipient of any given copy. In case sensitive information gets leaked to competitors, clients, or mass media, a small fragment is sufficient to establish a source of the leak.
An ability to identify the source of a leak in case someone takes a screenshot of sensitive data or photographs a computer screen is one of the critical advantages of the ILD-system.
According to a Forbes forecast, up to 83 percent of corporate data will be stored on cloud services in 2020. Yet, cloud services are not the most secure way to store sensitive data. Therefore, leaks from cloud-based services grow every year — for example, more than 70 percent of sensitive data leaked from cloud-based servers in 2018.
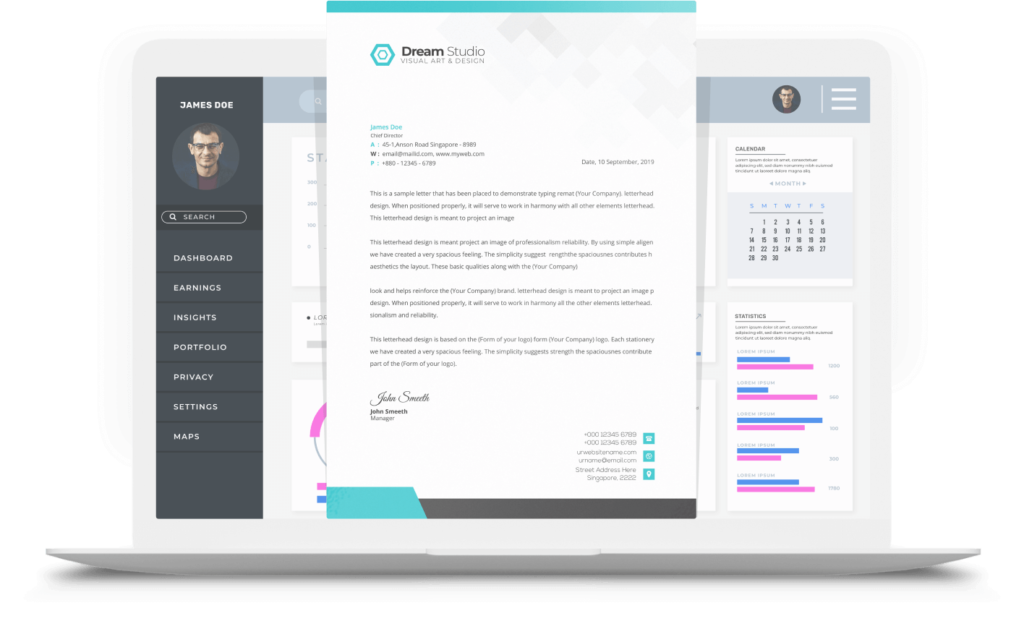
Virtual Data Room (VDR), a service that provides a high degree of protection against data leaks, can prevent such incidents. VDR is a cloud-based service for storing and sharing data; it provides its users with flexible access settings and fingerprints them.
The VDR system is based on the ILD technology and, therefore, allows the company to identify a specific source of a leak in case it happens. Its easy-to-use interface is convenient for most of the employees, as it is similar to the Google Drive interface.
A complex of measures that include prevention and introduction of new data protection technologies will help protect your company from corporate data leaks and, thus, significantly reduce the risk of reputational and financial losses.


















































