The pursuit of excellence and the desire to create a better and more intelligent world pushes companies to achieve. They come up with new solutions, bring them into reality, and transform people’s lives. In this spirit, the G-71 company took a step towards a safer and more honest world by presenting its own solution. More than 110 thousand corporate clients and two thousand individual users already use the LeaksID invisible marking system from G-71.
With LeaksID, they have the ability to determine if a leak has occurred, and who leaked their documents. How is this possible? Imagine you receive a confidential document. It looks like a regular file, with no artifacts, watermarks, or visible changes. But at the same time, it is marked with invisible marks. They are everywhere: in the margins, between the lines, in the letters. You don’t see them, but they are there.
So, if such a document is leaked, the owner of the original document will be able to determine exactly who did it, down to the name. Even if the document is torn, crumpled, or partially destroyed, a small fragment will be enough for the system to carry out recognition.
LeaksID can generate unique copies indefinitely, creating them automatically when people send documents by mail, print them, or send them to someone via a link.
Someone may receive such marked copies of confidential documents that can be distinguished from the originals. Then, any illegal activities performed with a document, particularly publishing it in an open forum, will be punishable.
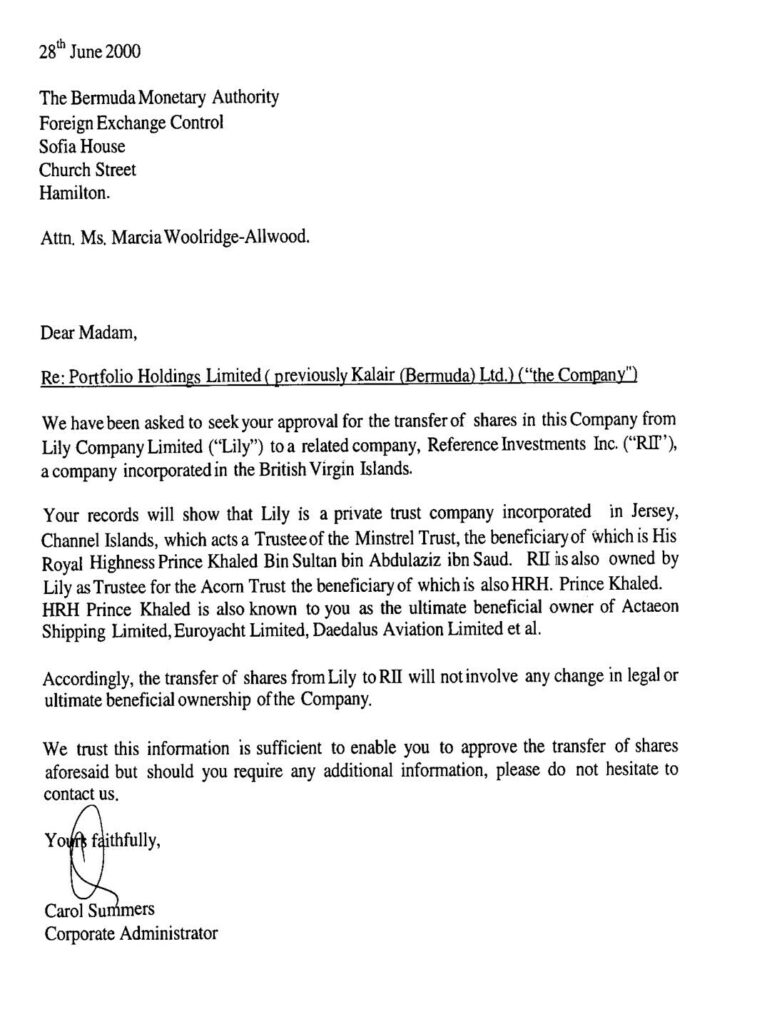
Please take a look at the document below. It’s labeled. Don’t believe it? If you now take a screenshot of it and post it somewhere, we will be able to recognize that the published compromised fragment was created precisely from this document from this article.
LeaksID was created to protect organizations such as medical institutions, law firms, consulting firms, telecom companies, and many more from leaks of sensitive documents. Every year, companies suffer a huge number of leaks, which significantly affect their reputation and financial performance. Not only is legal information leaked, but also personal data, patient and subscriber files, account information, etc.
After implementing LeaksID, users can be sure that all their documents are marked and protected, even from taking pictures with a smartphone or taking screenshots.
Suppose an unscrupulous person just takes a photo on his smartphone of a document that is opened on a computer screen and publishes it somewhere. In that case, LeaksID will be able to identify the source of the leak using that compromised fragment.
Any document can be marked, and everyone can be sure of the reliability of the recognition system. The next time you send sensitive documents to someone, just run them through the LeaksID online converter in advance. The system will create a unique copy of the original, and then you can send it to the right person. Or you can create a set of copies and send them to several recipients, but you’ll know in advance that if any of the copies are published somewhere, you will determine who’s guilty even by a fragment.
It will be impossible to remain unnoticed. All created and distributed copies are recorded.
It is hoped that with this technology, confidential document flow will become safer and more convenient, and the number of planned and accidental leaks will decrease. After all, where there is LeaksID, there is no place for criminal actions.


















































